Disable “application downloaded from the internet” Message on a Per-App Basis in Mac OS X | OSXDaily

Virus Bulletin on Twitter: "Sophos researcher @markloman writes about LockFile, a new ransomware family that emerged in July 2021. LockFile ransomware appears to exploit the ProxyShell vulnerabilities. https://t.co/RJ3V2ls1EM https://t.co/5OFlK0gapI ...

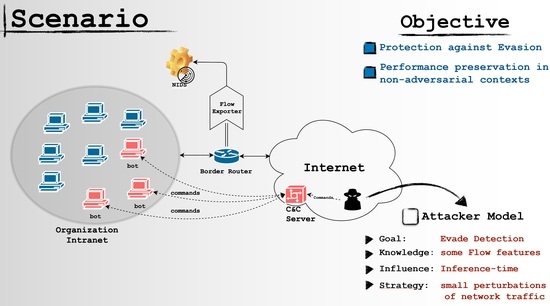
How to attack Machine Learning ( Evasion, Poisoning, Inference, Trojans, Backdoors) | by Alex Polyakov | Towards Data Science

Digital currencies, monetary sovereignty, and U.S.–China power competition - Huang - 2022 - Policy & Internet - Wiley Online Library








/cdn.vox-cdn.com/uploads/chorus_asset/file/15978252/flex2.jpg)





![Thinking Outside the Sand[box] Thinking Outside the Sand[box]](https://image.slidesharecdn.com/bsidesthinkingoutsidethesandbox-140223233924-phpapp01/85/thinking-outside-the-sandbox-17-320.jpg?cb=1393198896)


